
Andrea Danti - Fotolia
How to encrypt and secure a website using HTTPS
The web is moving to HTTPS. Find out how to encrypt websites using HTTPS to stop eavesdroppers from snooping around sensitive and restricted web data.
Encrypting web content is nothing new: It's been nearly 20 years since the publication of the specification for encrypting web content by running HTTP over the Transport Layer Security protocol. However, running a secure encrypted web server has gone from an option to a virtual necessity in recent years.
Attackers continue to seek -- and find -- ways to steal information sent between users and web services, often by tapping into unencrypted content being sent over the Hypertext Transfer Protocol. Even for mundane, untargeted web content, securing a website with encryption is crucial, as the top browsers now flag unencrypted websites as potentially dangerous.
While HTTPS website encryption is a requirement for assuring data integrity between browsers and servers, it is also increasingly a prerequisite for new browser functionality. Learning how to encrypt a website by enabling HTTPS is mandatory, especially for enterprises that want to provide users with a safe and secure web experience.
What is HTTPS?
HTTP transfers data as plain text between the client and server. Therefore, anyone who has access to any network segment between you and the server -- on your network, on the server's network or any place in between -- is able to view the contents of your web surfing.
Use HTTPS to protect data relating to financial transactions, personally identifiable information or any other sensitive data, as well as to avoid having browsers flag your site as insecure. HTTPS enables website encryption by running HTTP over the Transport Layer Security (TLS) protocol. Even though the SSL protocol was replaced 20 years ago by TLS, these certificates are still often referred to as SSL certificates.
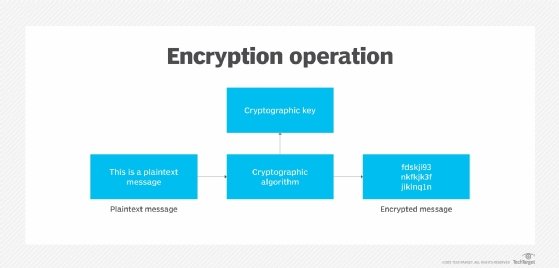
Here's a simplified view of how it works:
- You start your web browser and request a secure page by using the https:// prefix on the URL.
- Your web browser contacts the web server on the HTTPS port -- TCP port 443 -- and requests a secure connection.
- The server responds with a copy of its SSL certificate.
- Your web browser uses the certificate to verify the identity of the remote server and extract the remote server's public key.
- Your web browser creates a session key, encrypts it with the server's public key and sends the encrypted key to the server.
- The server uses its private key to decrypt the session key.
- The client and server use the session key to encrypt all further communications.
While HTTPS sessions can be reliably considered secure from eavesdropping attacks, HTTPS by itself does not protect against any other types of attack. Site administrators must still take an active role in preventing and mitigating cross-site scripting, injection and many other attacks that target application or other website vulnerabilities.
How to encrypt a website with HTTPS
The keys to encrypting a website reside, literally, in the web server. To enable a web server to encrypt all content that it sends, a public key certificate must be installed.
The details of installing an SSL certificate and enabling a web server to use it for HTTPS encryption vary depending on which web server software is being used. But, in almost all cases, the process broadly encompasses these steps:
- Identify all web servers and services that need to be encrypted. Servers may be hosted in the cloud, on premises, or at an internet service provider or other service provider. A single certificate could be used on multiple servers, but doing so can be risky: If the certificate is breached on one server, the attacker would be able to exploit the certificate on any other servers that use it. Best practice would be to get a separate certificate for each server or service.
- Get certificates for web servers and services that need them. Certificates can be purchased from a commercial certificate authority, or they may be acquired at no cost from Let's Encrypt, a free, open source and automated CA. Some commercial CAs also offer bare-bones or trial certificates at no charge, and some hosting service providers will provide certificates for customers whose websites are hosted on shared servers.
- Configure the web server to use HTTPS, rather than HTTP. The web server configuration process includes installing the SSL certificate, turning on support for HTTPS and configuring encryption options for HTTPS. The configuration process will vary depending on whether the server is hosted in the cloud or on premises and which web server software is in use.
- Administer and manage certificates. Ongoing administration and quality control over encrypted websites is critical. Qualys, a cloud security provider based in Foster City, Calif., offers an SSL server test page that can help. Certificates are issued with limited lifetimes that are typically one year and never for longer than 27 months. So, system administrators should regularly test and verify that certificates are valid and flag any that are nearing their end-of-life dates. Similarly, periodic testing should also be carried out to verify that servers are responding properly to valid requests and are fully protecting all data transmissions.
Installing a digital certificate and providing users with the ability to make HTTPS connections to your web server is one of the simplest ways you can add security to your website and build user confidence when conducting transactions with you over the web. It eliminates "site not secure" messages from web browsers and ensures communications are not subject to eavesdropping on the internet.






